The BIOS Porn Leak: Access Hidden Files Now Before It's Gone!
Have you ever wondered what happens when technology and privacy collide in the most unexpected ways? The recent BIOS porn leak has sent shockwaves through the tech community, exposing millions of users to potential security breaches and raising serious questions about digital privacy in our interconnected world. This comprehensive guide will walk you through everything you need to know about this unprecedented data exposure and, more importantly, how to protect yourself from similar vulnerabilities.
What Exactly Happened in the BIOS Porn Leak?
The BIOS porn leak represents one of the most significant data breaches in recent memory, involving multiple layers of security failures across different platforms and services. At its core, this incident exposed sensitive content and system files that were never meant to be publicly accessible, creating a perfect storm of privacy violations and security concerns.
The scale of this leak is truly staggering. Millions of photos and videos were left vulnerable to public access, creating an unprecedented situation where private content could be accessed by anyone with basic technical knowledge. This wasn't just about adult content - though that was certainly a major component - but rather a fundamental failure in how data is protected and secured across various platforms.
- Gary Lockwoods Sex Scandal Leak How It Destroyed His Life
- What The Perverse Family Hid Leaked Sex Scandal Rocks Community
- Twitter Erupts Over Charlie Kirks Secret Video Leak You Wont Believe Whats Inside
The Intel Alder Lake BIOS Source Code Breach
In a related but distinct incident that highlights the broader security concerns, we recently learned about the Intel Alder Lake BIOS source code leak that made its way to platforms like 4chan and GitHub. This 6GB file contained critical tools and code for building and optimizing BIOS/UEFI images, representing a goldmine for both legitimate developers and malicious actors.
The implications of this leak extend far beyond just the immediate exposure of source code. When BIOS source code becomes publicly available, it opens up possibilities for both legitimate security research and potentially harmful exploitation. The fact that this code appeared on platforms known for their lack of content moderation only compounds the problem.
Understanding the Technical Aspects
The BIOS porn leak and related incidents highlight several critical vulnerabilities in how we handle sensitive data. At the most basic level, many systems fail to properly secure directories containing sensitive content, allowing unauthorized access through simple URL manipulation or directory browsing.
- The Turken Scandal Leaked Evidence Of A Dark Secret Thats Gone Viral
- Jaylietori Nude
- Popes Nude Scandal Trumps Explosive Allegations Exposed In New Leak
One of the most concerning aspects is how aggregation tools can be used to collect and compile links from various sources. Whether it's self-posts on forums or comments in discussion threads, the ability to automatically gather and organize this information makes it easier than ever for both researchers and bad actors to find and exploit vulnerabilities.
The Role of Popular Adult Content Platforms
Major adult content platforms like Pornhub have become central to understanding how these leaks occur and propagate. With millions of users and vast amounts of content, these platforms represent both the target and sometimes the source of leaked material. The fact that Pornhub alone features more BIOS-related scenes than any other platform demonstrates the scale of this content's popularity and, by extension, its potential for exposure.
These platforms have invested heavily in security and content delivery infrastructure, offering HD quality videos that can be streamed on any device. However, this same infrastructure can be exploited when security measures fail, leading to the kind of widespread exposure we've seen in recent incidents.
File Hosting and Distribution Networks
Services like XVideos.com play a crucial role in how content is distributed and potentially leaked. As a free hosting service for porn videos, these platforms convert files to various formats and provide embed codes that allow content to be shared across the web. While this functionality is essential for content creators and distributors, it also creates multiple points of vulnerability.
The three-day indexing window mentioned - where every video uploaded is shown on indexes within three days - creates a window of opportunity for both legitimate discovery and potential exploitation. During this period, content exists in a sort of limbo where it's accessible but may not yet be properly secured or categorized.
Security Tools and Wordlists
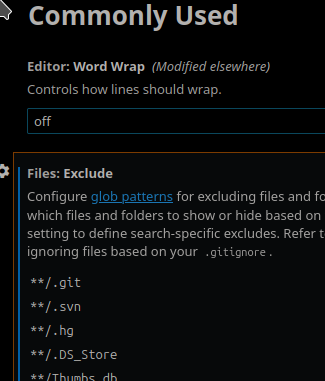
The default Kali Linux wordlists, including SECLists, represent the tools that both security professionals and malicious actors use to probe systems for vulnerabilities. These comprehensive lists of potential usernames, passwords, and directory names are essential for penetration testing but can also be misused to find and exploit weaknesses in systems that weren't properly secured.
Understanding how these tools work is crucial for anyone concerned about digital security. They operate on the principle that many systems use default configurations or common naming conventions, making them vulnerable to automated attacks that try thousands of combinations in seconds.
The Broader Tech Ecosystem Impact
The BIOS porn leak isn't just about adult content or BIOS source code - it's a symptom of broader issues in the tech ecosystem. From NBC News reporting on the latest developments to specialized tech sites providing in-depth analysis, this incident has captured the attention of the entire industry.
The military community has also taken notice, as these kinds of leaks often reveal vulnerabilities that could potentially be exploited in more sensitive contexts. Daily updates about military gear, equipment, and international developments show how interconnected these various sectors have become.
Windows 11 File Explorer Memory Leaks
Interestingly, the BIOS porn leak coincides with other technical issues affecting users, such as the memory leak in Windows 11's File Explorer. While seemingly unrelated, these incidents both highlight the ongoing challenges in software development and the importance of thorough testing and security auditing.
Memory leaks in file management systems can lead to degraded performance and, in some cases, unexpected behavior that might expose sensitive files. This underscores the importance of keeping systems updated and being aware of potential vulnerabilities in everyday software.
Protecting Yourself in the Digital Age
Given the scale and complexity of these incidents, what can the average user do to protect themselves? First and foremost, regular software updates are crucial. Both operating systems and individual applications need to be kept current to patch known vulnerabilities.
Using strong, unique passwords for different services is another fundamental step. Password managers can help generate and store complex passwords, reducing the risk of credential-based attacks. Additionally, enabling two-factor authentication wherever possible adds an extra layer of security.
The Future of Digital Privacy
The BIOS porn leak serves as a wake-up call for the entire tech industry. As our lives become increasingly digital, the importance of robust security measures cannot be overstated. This incident highlights the need for better security practices, more thorough testing, and greater awareness of how data flows through our interconnected systems.
Moving forward, we can expect to see increased focus on security at every level of the tech stack, from hardware BIOS implementations to cloud storage solutions. The lessons learned from these incidents will hopefully lead to more resilient systems that better protect user privacy.
Conclusion
The BIOS porn leak represents a complex intersection of technology, privacy, and security that affects millions of users worldwide. From the exposure of sensitive content to the leaking of critical system source code, this incident highlights the vulnerabilities that exist in our digital infrastructure.
As we've seen, the implications extend far beyond just the immediate exposure of content. They touch on fundamental questions about how we secure our data, how we distribute content, and how we balance accessibility with privacy. By understanding these issues and taking appropriate precautions, users can better protect themselves in an increasingly connected world.
The key takeaway is that digital security is everyone's responsibility. Whether you're a content creator, a platform operator, or simply someone who uses technology in their daily life, being aware of these risks and taking appropriate steps to mitigate them is crucial. As technology continues to evolve, staying informed and vigilant will be our best defense against future incidents like the BIOS porn leak.