Exclusive: How Sin Cos Tan Are Behind The Biggest Leak Of The Century!
In today's digital age, where our lives are increasingly intertwined with technology, a question looms large: How vulnerable are we to the next massive data breach? As we grapple with the aftermath of yet another colossal leak, it's becoming clear that the threat is not just imminent but already upon us. The recent revelations about a breach affecting billions of records have sent shockwaves through the cybersecurity community and raised serious concerns about our digital privacy. But what if we told you that the solution to this growing problem might lie in the most unlikely of places – the mathematical concepts of sine, cosine, and tangent? Join us as we unravel this complex web of data breaches and explore how these fundamental trigonometric functions could hold the key to our digital security.
The Anatomy of the Biggest Data Breach in History
Last week, cybernews reported on what is likely the biggest data leak to ever hit China, involving billions of documents with financial data, WeChat and Alipay details, as well as other sensitive personal data. This monumental breach has sent shockwaves through the global cybersecurity community, highlighting the ever-increasing scale and sophistication of cyber attacks.
The leak, which came to light in early 2024, reportedly exposed a staggering amount of personal and financial information. Sources close to the investigation suggest that the breach may have originated from a compromised government database, potentially giving hackers access to a treasure trove of sensitive data. The full extent of the damage is still being assessed, but initial estimates indicate that the personal information of hundreds of millions of individuals may have been compromised.
- Eva Violet Nude
- Leaked Porn Found In Peach Jars This Discovery Will Blow Your Mind
- Cheapassgamer Twitter
This breach is particularly concerning due to the nature of the data involved. Financial records, payment platform details, and other sensitive personal information can be exploited for various malicious purposes, including identity theft, financial fraud, and targeted phishing attacks. The potential for long-term damage to individuals and businesses alike is immense, underscoring the critical need for robust cybersecurity measures.
A Timeline of Major Data Breaches
To put this latest breach into perspective, it's worth examining the broader context of data security incidents over the past few years. Last summer, the largest password compilation with nearly ten billion unique passwords, RockYou2024, was leaked on a popular hacking forum. This massive dataset, compiled from various sources, represents a significant threat to online security, as it provides cybercriminals with a vast array of potential credentials to test against various online services.
The RockYou2024 leak is particularly troubling because it demonstrates how individual data breaches, while serious on their own, can be combined to create even more powerful tools for hackers. By aggregating data from multiple sources, cybercriminals can increase their chances of successfully breaching accounts through credential stuffing attacks, where they attempt to use known username and password combinations across multiple platforms.
- Exposed Janine Lindemulders Hidden Sex Tape Leak What They Dont Want You To See
- Penny Barber
- Sherilyn Fenns Leaked Nudes The Scandal That Broke The Internet
This trend of increasingly large and comprehensive data leaks highlights the need for a paradigm shift in how we approach online security. Traditional methods of protecting individual accounts are no longer sufficient in the face of such massive data compilations. We need to explore new, more robust approaches to safeguarding our digital identities.
The Global Impact of Massive Data Breaches
A staggering 16 billion records have just been leaked in the biggest data breach in history, exposing credentials from major global platforms. This unprecedented leak has far-reaching consequences that extend well beyond the immediate victims of the breach.
The sheer scale of this breach is difficult to comprehend. To put it into perspective, if each record represented a single sheet of paper, the stack would reach over 1,000 miles high – more than four times the height of Mount Everest. This visualization helps underscore the enormity of the data now potentially in the hands of cybercriminals.
The impact of such a massive breach is multifaceted. For individuals, it means an increased risk of identity theft, financial fraud, and targeted phishing attacks. For businesses, it can lead to significant financial losses, reputational damage, and potential legal liabilities. On a broader scale, it can undermine public trust in digital services and potentially impact economic stability.
One of the largest data breaches in history has now occurred, exposing Facebook, Apple, Google, and over 30 more websites' passwords. This particular breach is especially concerning due to the prominence of the affected platforms and the potential for widespread exploitation.
The exposure of credentials from these major tech companies is particularly troubling because of the interconnected nature of our digital lives. Many users employ the same or similar passwords across multiple platforms, meaning that a single breach can have cascading effects across their entire online presence. This "domino effect" of credential reuse significantly amplifies the potential damage of large-scale data breaches.
Understanding the Cybersecurity Landscape
A deep dive into global data breaches is essential in today's interconnected world, where cybersecurity incidents are not a matter of if, but when. The frequency and severity of data breaches have been steadily increasing over the past decade, driven by factors such as the growing value of data, the increasing sophistication of cybercriminals, and the expanding attack surface created by the proliferation of internet-connected devices.
Some of the largest, most damaging breaches of 2024 already account for over a billion stolen records. This statistic is a stark reminder of the ongoing challenges faced by organizations in protecting sensitive data. It also highlights the need for a more proactive and comprehensive approach to cybersecurity.
To better understand the current landscape, it's helpful to examine the common characteristics of major data breaches:
Sophisticated attack vectors: Cybercriminals are increasingly using advanced techniques such as zero-day exploits, social engineering, and supply chain attacks to gain unauthorized access to systems.
Insider threats: A significant portion of data breaches involve current or former employees who misuse their access to sensitive information.
Third-party vulnerabilities: Many breaches occur through vulnerabilities in third-party systems or services that organizations rely on.
Inadequate security measures: In many cases, breaches occur due to basic security failures such as weak passwords, unpatched software, or misconfigured systems.
Data monetization: The underground economy for stolen data has grown significantly, providing a strong financial incentive for cybercriminals to continue their activities.
The Role of Whistleblowing in the Digital Age
While data breaches are generally viewed as malicious acts, it's worth considering the role of whistleblowing in exposing wrongdoing and promoting transparency. Julian Assange, a founding member of the WikiLeaks staff, has been a controversial figure in this regard. WikiLeaks, established in Australia with the help of Daniel Mathews, has been at the center of numerous high-profile information leaks over the past decade.
The inspiration for WikiLeaks was Daniel Ellsberg's release of the Pentagon Papers in 1971, which exposed government secrets related to the Vietnam War. Assange built WikiLeaks to shorten the time between a leak and its coverage by the media, leveraging the power of the internet to rapidly disseminate information.
Wikileaks was established in Australia with the help of Daniel Mathews and its servers were soon moved to Sweden and other countries that provided. This global approach to hosting was designed to protect the organization from legal challenges and ensure the continued availability of leaked information.
While the activities of WikiLeaks are distinct from criminal data breaches, they highlight the complex ethical and legal issues surrounding the release of sensitive information. The tension between the public's right to know and the need to protect sensitive data remains a contentious issue in the digital age.
The Mathematical Solution: Sine, Cosine, and Tangent
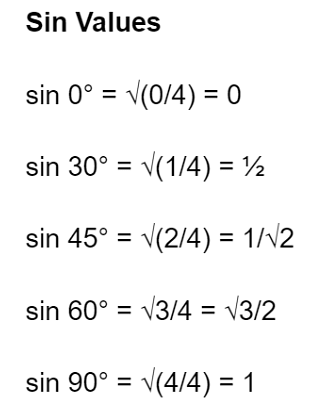
Now, let's explore the intriguing connection between fundamental mathematical concepts and data security. The trigonometric functions sine, cosine, and tangent – often abbreviated as sin, cos, and tan – may seem unrelated to cybersecurity at first glance. However, these functions form the basis of many advanced encryption algorithms and cryptographic protocols.
Sine, cosine, and tangent are periodic functions that describe the relationships between angles and sides in a right triangle. These functions have unique properties that make them valuable in various fields, including signal processing, physics, and yes, cryptography.
In the context of data security, these functions can be used to create complex, non-linear transformations of data. This property is particularly useful in developing encryption algorithms that are resistant to common attack methods. For example, the use of sine and cosine functions in certain encryption schemes can create patterns that are extremely difficult for attackers to predict or reverse-engineer.
Moreover, the periodic nature of these functions can be leveraged to create keys that change over time, adding an extra layer of security to encryption systems. This approach, known as time-based key rotation, can significantly reduce the window of opportunity for attackers to exploit stolen credentials.
Implementing Advanced Security Measures
To protect against the ever-growing threat of data breaches, organizations and individuals must adopt a multi-faceted approach to cybersecurity. Here are some advanced security measures that incorporate mathematical concepts and cutting-edge technologies:
Elliptic Curve Cryptography (ECC): This form of public-key cryptography is based on the algebraic structure of elliptic curves over finite fields. ECC offers strong security with smaller key sizes compared to traditional methods, making it more efficient for resource-constrained devices.
Quantum Key Distribution (QKD): As quantum computing threatens to break many current encryption methods, QKD uses the principles of quantum mechanics to create theoretically unbreakable encryption keys.
Homomorphic Encryption: This advanced form of encryption allows computations to be performed on encrypted data without decrypting it first, potentially revolutionizing how we handle sensitive information in cloud environments.
Blockchain Technology: The decentralized and immutable nature of blockchain can be used to create secure, transparent systems for managing digital identities and access controls.
Artificial Intelligence and Machine Learning: AI and ML algorithms can be used to detect anomalies in network traffic, identify potential threats, and respond to security incidents in real-time.
Zero Trust Architecture: This security model assumes no trust by default, requiring verification for every user and device attempting to access resources, regardless of their location or network.
The Future of Data Security
As we look to the future, it's clear that the battle between cybercriminals and cybersecurity professionals will continue to intensify. The increasing value of data, the growing sophistication of attack methods, and the expanding attack surface created by the Internet of Things (IoT) all point to a future where robust security measures are not just important, but essential.
Emerging technologies such as quantum computing and 5G networks will bring new opportunities and challenges to the field of cybersecurity. Quantum computers, while still in their early stages, have the potential to break many current encryption methods, necessitating the development of quantum-resistant algorithms. On the other hand, 5G networks will enable faster, more connected systems, but also create new vulnerabilities that need to be addressed.
In this evolving landscape, the role of mathematics – including the seemingly simple concepts of sine, cosine, and tangent – will remain crucial. As we develop more advanced encryption methods and security protocols, the fundamental principles of mathematics will continue to underpin our efforts to protect sensitive data.
Conclusion
The recent wave of massive data breaches has laid bare the vulnerabilities in our current approach to data security. From the billions of records exposed in the latest Chinese leak to the RockYou2024 password compilation, it's clear that we are facing an unprecedented challenge in protecting sensitive information.
However, by understanding the nature of these threats and leveraging advanced mathematical concepts and emerging technologies, we can develop more robust defenses against cyber attacks. The connection between trigonometric functions like sine, cosine, and tangent and modern cryptography may seem tenuous at first, but it underscores the importance of fundamental mathematical principles in our ongoing battle for data security.
As we move forward, it's crucial that individuals, organizations, and governments alike prioritize cybersecurity and invest in the development of more advanced protection measures. Only by staying ahead of the curve and embracing innovative approaches to data security can we hope to safeguard our digital future in an increasingly connected world.